Learn more about how ARGOS works and how it supports individual Consultants, and Security and Cloud Operations teams in securing the cloud.
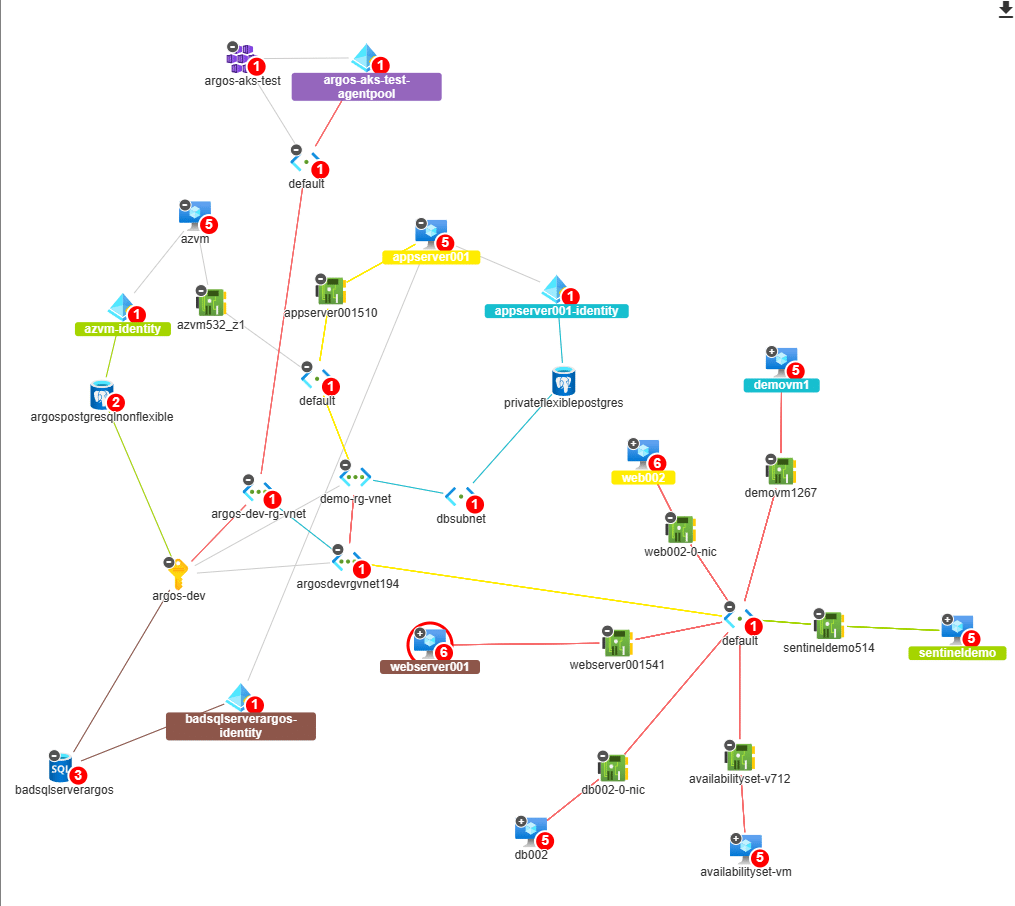
Understand Blast Radius
ARGOS Cloud Diagrams visually display the surrounding architecture so that teams can quickly identify and understand security issues and their impact, also known as blast radius.
Additional checks also display lateral movement opportunities for threat actors.
This offers you CSPM, CAASM, and CIEM capabilities in one place.
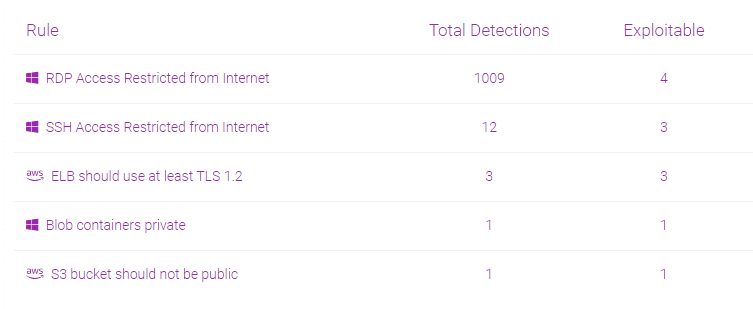
Detect Security Issues
ARGOS applies the critical knowledge Security Teams require to identity actual security problems in the public cloud.
Publicly exposed assets are identified automatically and are ready for further investigation.
Agentless monitoring
ARGOS is completely agentless, requires no installation of any kind of software in order to monitor any cloud environment.
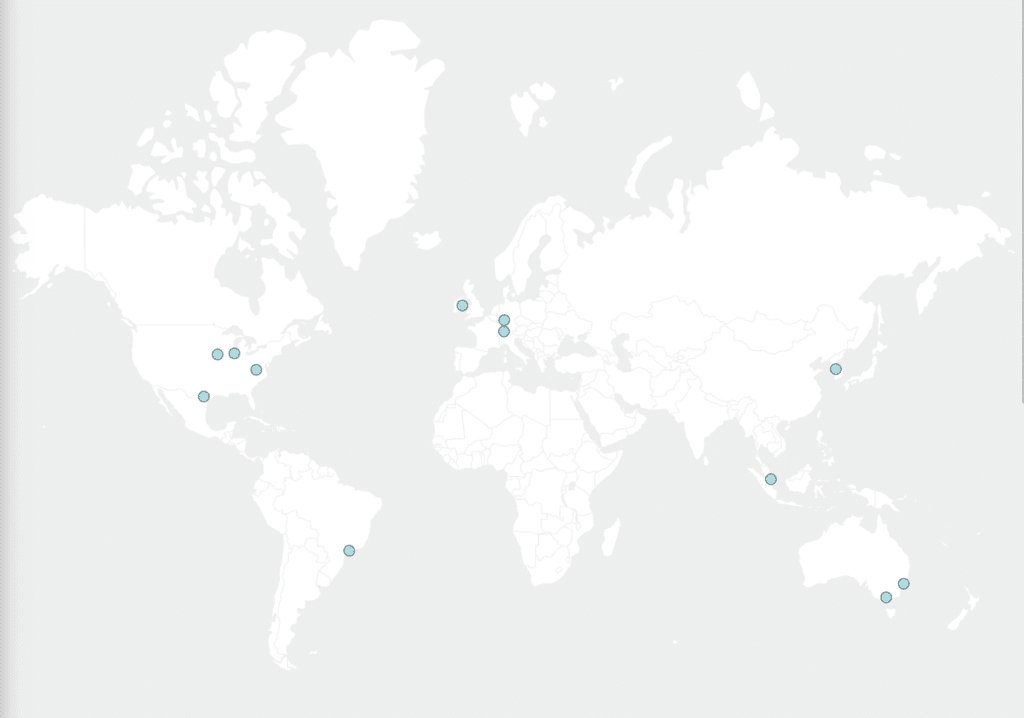
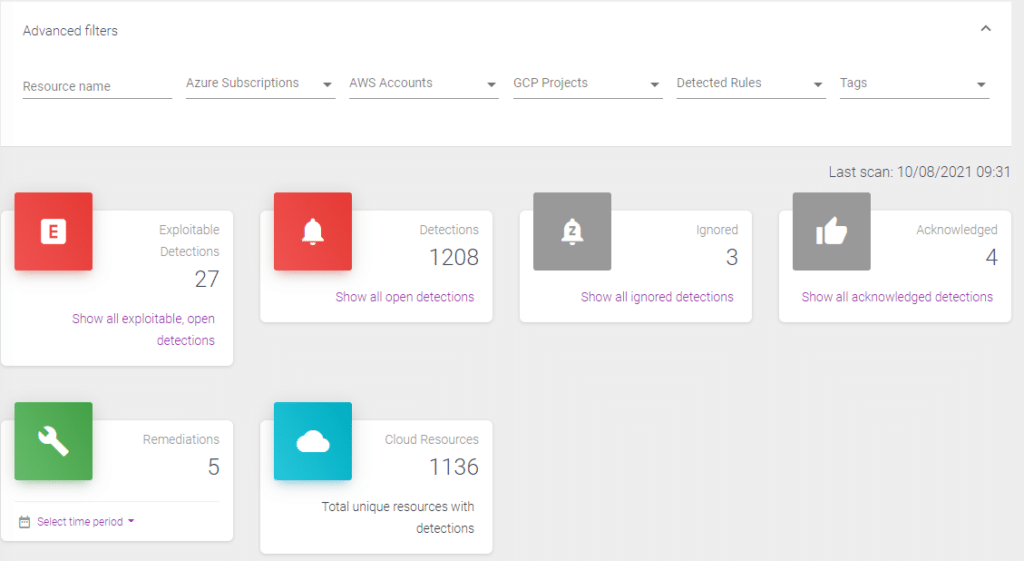
Multi-cloud visibility
(for Service Providers)
Gain visibility of the security posture of multi-cloud environments and complex architectures using flexible filters that apply across Azure, AWS and GCP.
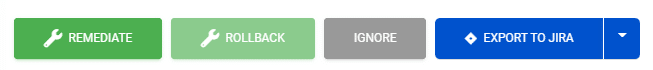
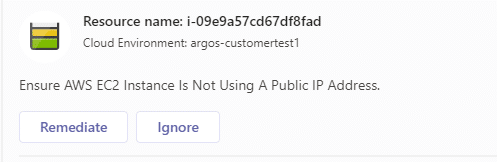
Fix Issues
(for Service Providers)
Built-in remediation capability without the need to deploy any extra infrastructure ensures that issues are fixed promptly.
With the click of a button or simple API call ARGOS can fix cloud security issues in seconds.
If required, ARGOS can also roll back changes it made.
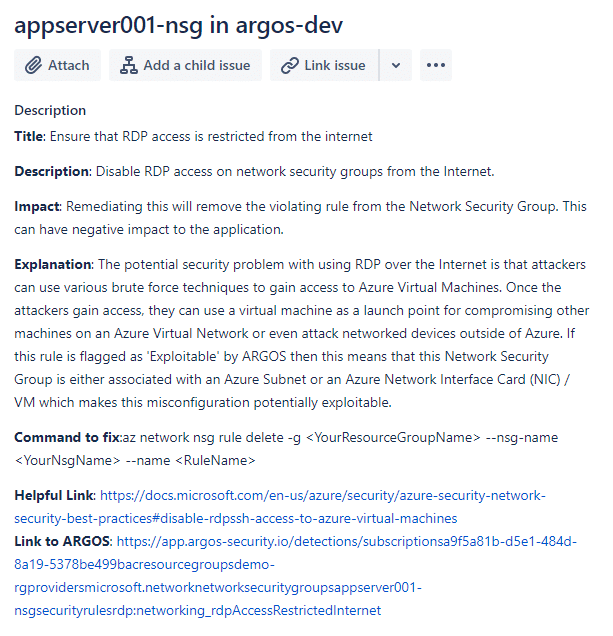
ITSM Integration
(for Service Providers)
ARGOS easily integrates into Atlassian Jira and ServiceNow to ensure that all issues are tracked and audited in your ITSM system.
Tickets can be easily opened from within ARGOS and then assigned to the correct team members to remediate the security issue.
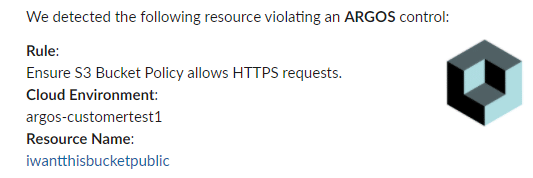
Chat integration
(for Service Providers)
In just a few clicks ARGOS can send notifications to teams on Slack or Microsoft Teams.
It is simple to configure and ensures that busy teams are not swamped by meaningless alerts.
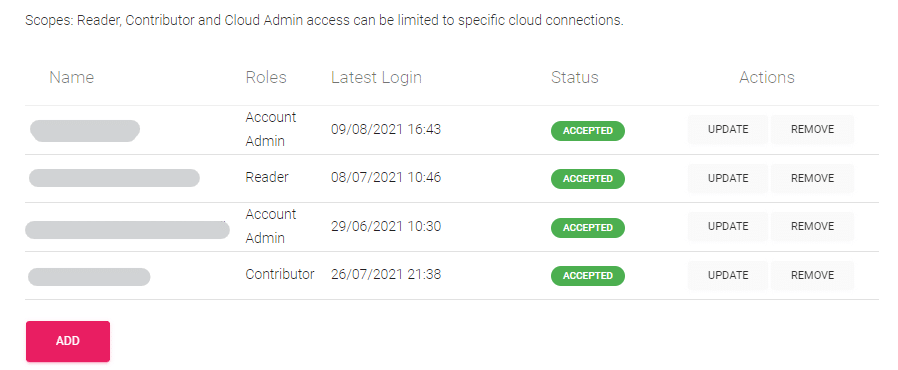
Role-based access
(for Service Providers)
Give unlimited team members, even your customers, access to ARGOS and assign just the right permissions to them.
The ability to scope permissions to specific environments means that individuals can only see what they are meant to see.
ARGOS assisted to detect and decommission an unused Azure FTP resource that was highly vulnerable and present in our environment for quite a while. – Security Architect, large Australian construction company
Twenty-two exploitable and High-Risk vulnerabilities have been mitigated in just two days. – Security Engineer, Australian retailer
